So how do we get VPN / Gateway diagnostics out of Azure these days if we are using an ARM based virtual network ? Well we need to run a script in Azure PowerShell (v1.0 or later) to collect diagnostics.
How do I Get Gateway VPN Diagnostics for an Azure ARM VNET ?
I have put this together as it took me a while to find it and get my script working so I have modified it and made it simpler for me at least to use in the future as part of my toolkit so feel free to do the same.
In this article I will show how you can pull out diagnostic data from the Azure platform for an ARM based virtual network gateway which could be useful for troubleshooting VPN issues.
The script uses the original post by Keith Mayer but I have added another check to it and some variables at the top which may make it a bit easier to use.
Why Do We Need Azure VPN Gateway Diagnostics ?
Well if you are having trouble setting up your VPN device and you wish to check what’s going on at the Microsoft side then this will come in very handy. If you are planning to raise a support call with Microsoft then they may well ask for this so it would be in your interest to set this up first and provide this as part of your support ticket to help speed things up.
What Can Possibly Go wrong ?
In most cases the problem is at the customer VPN side as there is very little or nothing we can specify on the Microsoft side in terms of the actual VPN settings. Here is some further reading on the limited gateway options we have. https://azure.microsoft.com/en-gb/documentation/articles/vpn-gateway-about-vpngateways/.
Her e are some of the gateway properties we can specify the following items :-
- Dynamic Gateway IP (Given by Azure!)
- Pre Shared Key
- Gateway Type – Routebased or Policybased
- VPN Type – VPN or ExpressRoute
- Gateway SKU – Basic, Standard or High Performance
As you can see we have no control over IKE settings, timeouts, encryption levels etc. However the customer may have any type of supported (or not) device such as a CISCO ASA, ASR, Juniper, Checkpoint etc. Each one of these have their own GUI’s and settings for VPN connections which can be difficult to get just right and this is another reason why gathering as much info as possible from the Azure side may help. Full compatible device details are provided here :- https://azure.microsoft.com/en-gb/documentation/articles/vpn-gateway-about-vpn-devices/. Some have links to setup instructions and samples. This link also provides specific settings such as IKE and IPSEC. This is the info that is provided by Microsoft to help get your VPN device up and running. If all is looking ok on the Microsoft side then the customer may need to contact their VPN device vendor if they are not able to establish a connection.
Here is the script
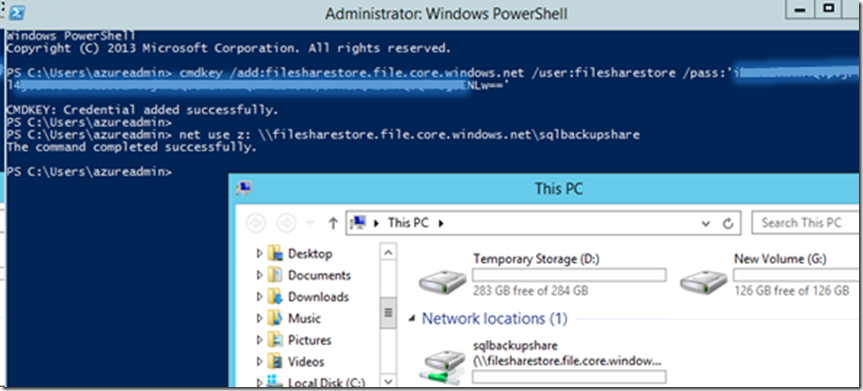
The first step is to connect to your subscription in both Resource Manager (RM) AND Service Manager (SM). It also requires you have Azure PowerShell module version 1.0 or above. The reason for using both Azure models (SM and RM) is that the VPN diagnostics are only available on the older SM platform.
# This script downloads gateway diagnostic data for a VPN Gateway inside an Azure Virtual Network
# Original Script provided by Keith Mayer of Microsoft
# http://blogs.technet.com/b/keithmayer/archive/2015/12/07/step-by-step-capturing-azure-resource-manager-arm-vnet-gateway-diagnostic-logs.aspx
# Modified by Mitesh Chauhan (miteshc.wordpress.com) slightly to add some variables and only get provisioned state gateway.
# STEP 1 – SIGN IN TO BOTH Azure SM and RM
$SubscriptionID = “Your Sub ID”
$cred = Get-Credential
# Sign-in to Azure via Azure Resource Manager and also Sign into Azure Service Manager
# Set up Azure Resource Manager Connection
Login-AzureRmAccount -Credential $cred
Select-AzureRmSubscription -SubscriptionId $subscriptionId
# Set up Service Manager Connection – Required as gateway diagnostics are still running on Service Manager and not ARM as yet.
Add-AzureAccount -Credential $cred
Select-AzureSubscription -SubscriptionId $subscriptionId
# VNET Resource Group and Name
$rgName = ‘RG NAME’
$vnetGwName = “Gateway Name”
$timestamp = get-date -uFormat “%d%m%y@%H%M%S”
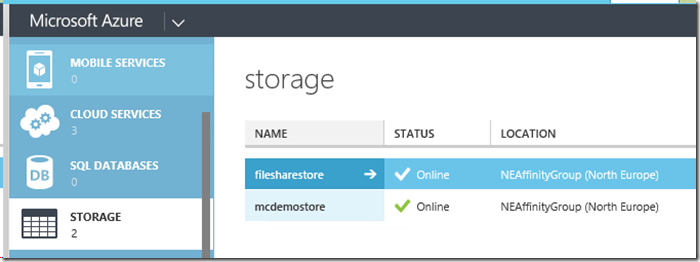
# Details of existing Storage Account that will be used to collect the logs
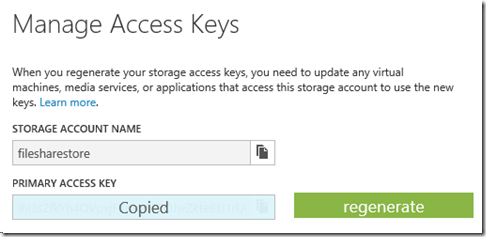
$storageAccountName = “Storage account”
$storageAccountKey = ‘KEY HERE’
$captureDuration = 60
$storageContainer = “vpnlogs”
$logDownloadPath = “C:\Temp”
$Logfilename = “VPNDiagLog_” + $vnetGwName + “_” + $timestamp + “.txt”
# Set Storage Context and VNET Gateway ID
$storageContext = New-AzureStorageContext -StorageAccountName $storageAccountName -StorageAccountKey $storageAccountKey
# NOTE: This is an Azure Service Manager cmdlet and so no AzureRM on this one. AzureRM will not work as we don’t get the gatewayID with it.
$vnetGws = Get-AzureVirtualNetworkGateway
# Show Details of Gateway
$vnetGws
# Added check for only provisioned gateways as older deleted gateways of same name can also appear in results and capture will fail
$vnetGwId = ($vnetGws | ? GatewayName -eq $vnetGwName | ? state -EQ “provisioned”).GatewayID
# Start Azure VNET Gateway logging
Start-AzureVirtualNetworkGatewayDiagnostics `
-GatewayId $vnetGwId `
-CaptureDurationInSeconds $captureDuration `
-StorageContext $storageContext `
-ContainerName $storageContainer
# Optional – Test VNET gateway connection to another server across the tunnel
# Only use this if you are connected to the local network you are connecting to FROM Azure. Otherwise create some traffic across the link from on prem.
# Test-NetConnection -ComputerName 10.0.0.4 -CommonTCPPort RDP
# Wait for diagnostics capturing to complete
Sleep -Seconds $captureDuration
# Step 6 – Download VNET gateway diagnostics log
$logUrl = ( Get-AzureVirtualNetworkGatewayDiagnostics -GatewayId $vnetGwId).DiagnosticsUrl
$logContent = (Invoke-WebRequest -Uri $logUrl).RawContent
$logContent | Out-File -FilePath $logDownloadPath\$Logfilename
I hope you found this information and script useful.
Thank you for visiting !








![image_thumb[19] image_thumb[19]](https://miteshc.files.wordpress.com/2014/11/image_thumb19_thumb.png?w=480&h=351)
![image_thumb[23] image_thumb[23]](https://miteshc.files.wordpress.com/2014/11/image_thumb23_thumb.png?w=529&h=271)
![image_thumb[30] image_thumb[30]](https://miteshc.files.wordpress.com/2014/11/image_thumb30_thumb.png?w=302&h=364)
![image_thumb[32] image_thumb[32]](https://miteshc.files.wordpress.com/2014/11/image_thumb32_thumb.png?w=465&h=259)
![image_thumb[34] image_thumb[34]](https://miteshc.files.wordpress.com/2014/11/image_thumb34_thumb.png?w=470&h=173)
![image_thumb[36] image_thumb[36]](https://miteshc.files.wordpress.com/2014/11/image_thumb36_thumb.png?w=420&h=158)
![image_thumb[25] image_thumb[25]](https://miteshc.files.wordpress.com/2014/11/image_thumb25_thumb.png?w=501&h=346)